Before we talk about Origin IP you must have to know about CDN.
So what is CDN?
Let’s consider you have a website and there are so many contents or resources in your website and you’re in Delhi and you’ve requested an image on a server in Singapore, which is 6000 miles away. It may typically take around 350-400 milliseconds to send the request and receive the response.
If you were to request the same image from a server in Gurgaon, that is about 45 Kilometers from Delhi, it may take about 10-15 milliseconds to send the request and obtain the response. That’s 25-30 times higher than the previous case. However as a result of we’re speaking in terms of milliseconds the difference could be unperceivable.
However, it hardly perceptible difference is large once one considers that a typical webpage will include over 2 megabytes of data spread across thirty requests. because browsers only create a small number of coinciding requests and every request could involve many round-trips to the server, these milliseconds add up to several seconds, makes the website slow.
So the major reason is to use a CDN is it provides the best performance efficiently and loads the images, CSS files and other resources or contents of the websites quickly.
Here are some advantages of Using a CDN:
Helps to reduce bandwidth costs.
Helps to improve in Website Security.
Helps to improve in SEO.
Helps to improve in incoming and outgoing traffics and scalability.
Helps to improve in better conversion rates
What is Reverse Proxy?
According to cloudflare A reverse proxy is a server that sits in front of web servers and forwards client (e.g. web browser) requests to those web servers. Reverse proxies are typically implemented to help increase security, performance, and reliability.
What is CDN Security?
CDNs by themselves cannot block bad bots from infecting a website, CDNs are vulnerable on their own, which is why you need to use a WAF. A Web Application Firewall helps protect web applications by filtering and monitoring HTTP traffic between a web application and the Internet. It typically protects web applications from some popular attacks such as XSS (Cross Site Scripting), SQL Injection, DDoS and other attacks.
What is Origin IP
Most of the websites use the protections mentioned above to hide their Origin IP to prevent attackers from DDoS attacks, and other malicious things attackers can do.
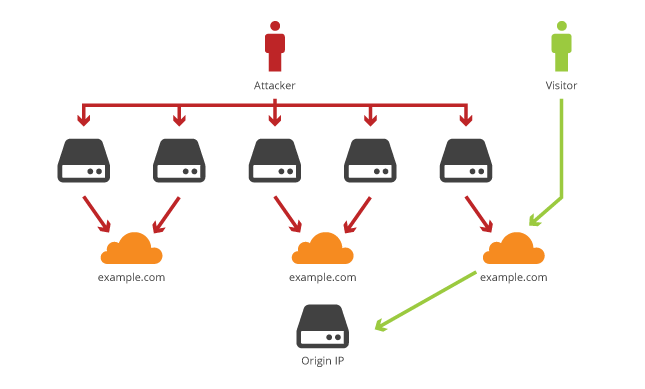
Impact of getting access to the Origin IP
Once you have the Origin IP of a website you can bypass all the protections which is Provided by the particular CDN Provider. It could enable MITM, DDoS and other attacks.
How to find and verify Origin IP of a website
- Go to censys.io
- Search keyword “example.com”
- The URL permalink will be look like: “https://censys.io/ipv4?q=example.com“
- Scroll Down below you found Original IP Revealed e.g. 44.78.195.155.
- Now if you can access the contents of the real website using this origin IP then it is vulnerable to Origin IP disclosure vulnerability.
- Also there is a tool called Cloudflair where you can automate to find the Origin IP of a website if that is vulnerable.
Note: Here I mentioned example.com for demonstration purposes, you can check of any website.
I hope you find this article helpful. If you like this post then don’t forget to share it with others.
Have a nice stay there!


